A Breakthrough in IoT Authentication
Most security systems protect a secret — a key, a password, something static that gets used over and over. The attacker's job is to find that secret. Once they have it, they're in forever.
ZipIPS™ doesn't work that way.
Every authentication credential is tied to a single, unrepeatable moment in time. Both devices independently derive the credential from pre-shared tables that never cross the network. There is no static key to steal. No credential to replay. Authentication works both ways — the client verifies the host and the host verifies the client, each generating a fresh timestamp and independently confirming the response before access proceeds. And any device can challenge the commanding host before executing a new instruction — blocking man-in-the-middle attacks before they start. Failed attempts are immediately blocked, permanently logged, and available for review.
This is Zero Trust at the device level: never trust, always verify.
ZipIPS™ is protected by two issued U.S. patents — US10171465B2 and US10348729B2 — invented by Helene E. Schmidt of Creative Synergies LLC. It is a licensable architecture, not a product. Licensees write their own implementation code, configured for their specific environment, at millisecond, microsecond, or nanosecond precision depending on their hardware capabilities.
Independent analyses by Claude (Anthropic) and Grok 4 (xAI) — conducted separately and reaching the same conclusions — confirm that ZipIPS™ delivers greater security than current NIST post-quantum and lightweight cryptography standards, in a credential one-eighth the size of CRYSTALS-Kyber-512.
How ZipIPS™ Compares
Click either chart to enlarge
NIST Security Level Comparison: Bits of Security
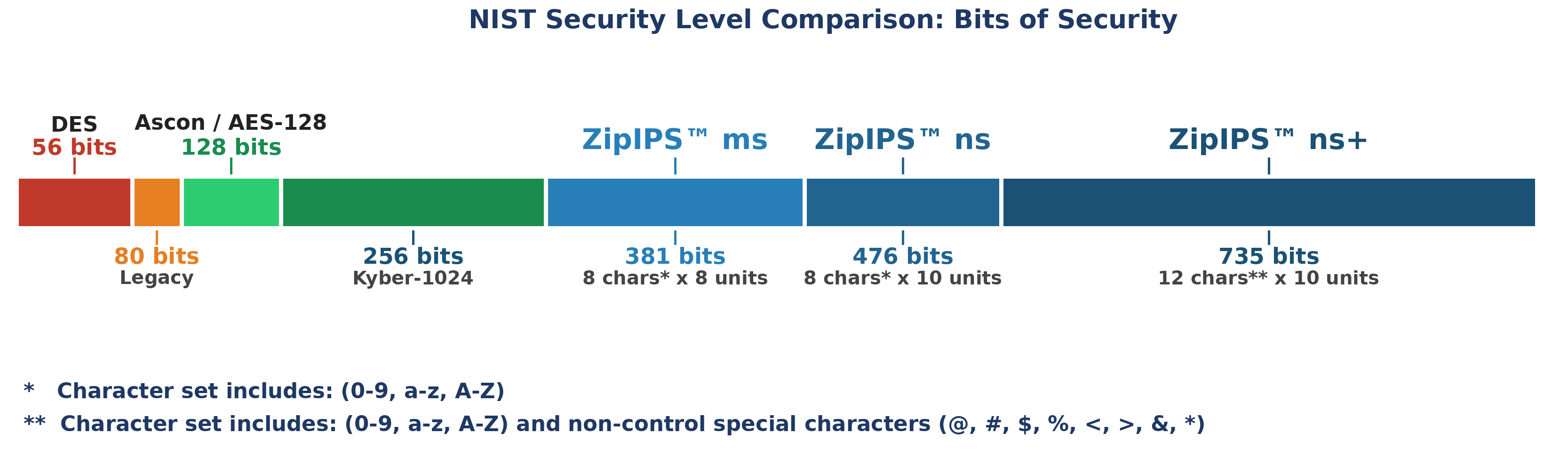
ZipIPS™ ms (381 bits) · ns (476 bits) · ns+ (735 bits) — compared to DES, AES-128, and CRYSTALS-Kyber-1024
Credential Size Comparison: Bytes per Authentication
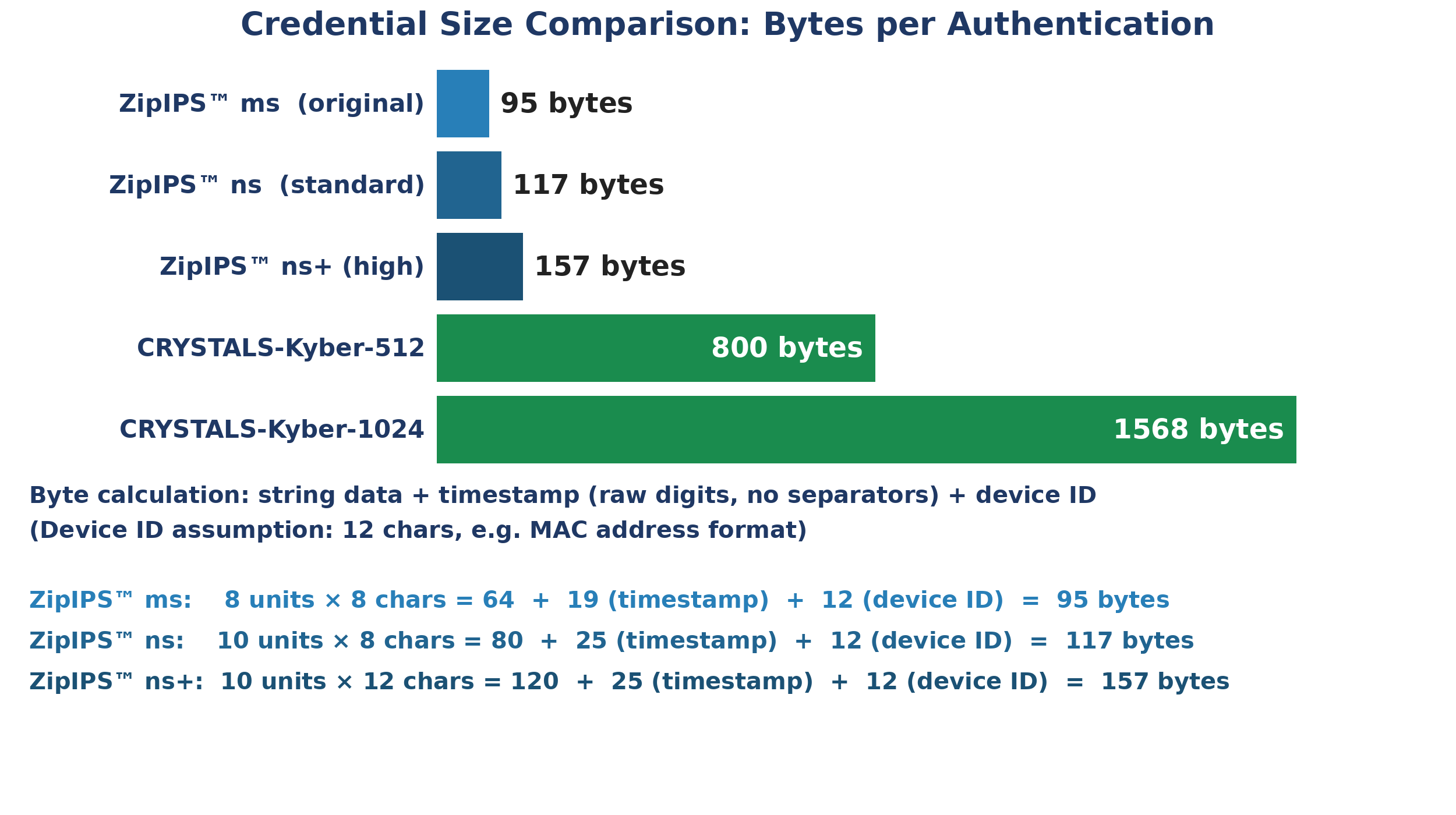
ZipIPS™ credentials (95–157 bytes) vs. CRYSTALS-Kyber-512 (800 bytes) and Kyber-1024 (1,568 bytes)
Applications of ZipIPS™
ZipIPS™ applies wherever device-level authentication is required. White Papers are available for each of the following categories, providing in-depth technical and commercial insights.
- Aerospace and Space
- Agentic AI
- AI and Edge Computing
- Autonomous Vehicles
- Banking and Financial Services
- Consumer IoT
- Defense Systems
- Education and Research
- Government and Public Sector
- Healthcare IoT
- Manufacturing
- Media
- Quantum Infrastructure
- Retail and E-Commerce
- Smart Cities
- Smart Grids and Energy Infrastructure
- Sports and Entertainment
- Telecommunications
- Transportation
ZipIPS™ is available for licensing. Please visit more pages on this site and Contact Us if you have any questions.